Apple has started sending out rooted iPhones to participants of its Security Research Device Program. These special iPhones allow feature code execution access which is not available in normal iPhones available to consumers. The devices are intended to help with security research and development.
The iPhones will be loaded to the security researchers for one year, but the duration can be extended upon request. These researchers are selected participants by Apple and will help with increasing the security of iOS and iPhone in general.
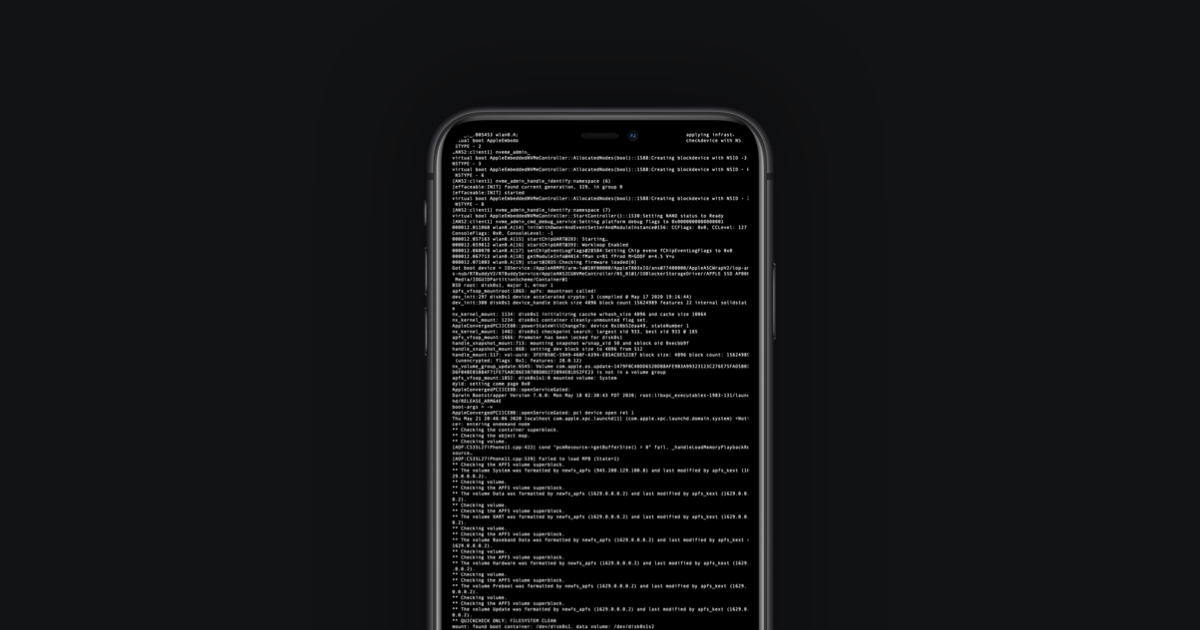
Participants start receiving special iPhones from Apple as part of Security Research Device Program
Apple explains its SRD program as following:
As part of Apple’s commitment to security, this program is designed to help improve security for all iOS users, bring more researchers to iPhone, and improve efficiency for those who already work on iOS security. It features an iPhone dedicated exclusively to security research, with unique code execution and containment policies.
Apple requires that these iPhones are kept in secure locations, and not used for personal usage. Access should be limited to only the people that are authorized by Apple to use these devices. These devices will provide shell access, and allow installation of any app or tool, without the need to ‘jailbreak’ them, which is why these iPhones will have to be kept safe at all times.
Companies like Apple usually have bug bounty programs to encourage and reward researchers to find and share security flaws with them. This helps in continuous improvement to operating systems and platforms, as security is always a cat and mouse game between companies and hackers and groups with malicious intents.
The Security Research Device Program was announced back in July. Participants in the SRD program are expected to share any bugs that they find with Apple. Researchers who reports security issues to Apple will be eligible for the company’s bounty reward program, which features rewards up to $1.5 million.
Apple has been criticized in the past for not working well with security researchers. With its on-going bounty program and this new device program, the company has taken major steps towards working closely with researchers to help further improve security of its devices.




2 comments