Scam apps find one or the other to fool the App Store Review team and rob users of hundreds and thousands of dollars. The problem is even worse on Google Play Store.
New research by HUMAN’s Satori Threat Intelligence team found 10 ad-fraud apps on App Store and 75 apps on Google Play Store. These scam apps flood mobile users with advertisements “both visible and hidden” and also impersonate legitimate apps to generate revenue.
Collectively the Adware has been installed 13 million times.
Google Play Store has 7x more Adware than App Store
According to the report shared by Bleepingcomputer, the fraudulent apps are part of the third wave of ad fraud campaign called “Scylla” launched by the same threat actor who was behind “Poseidon”, an operation found in August 2019. Its second wave called Charybdis “culminated towards the end of 2020.”
75 applications on Google Play and another ten on Apple’s App Store engaged in ad fraud. Collectively, they add to 13 million installations.
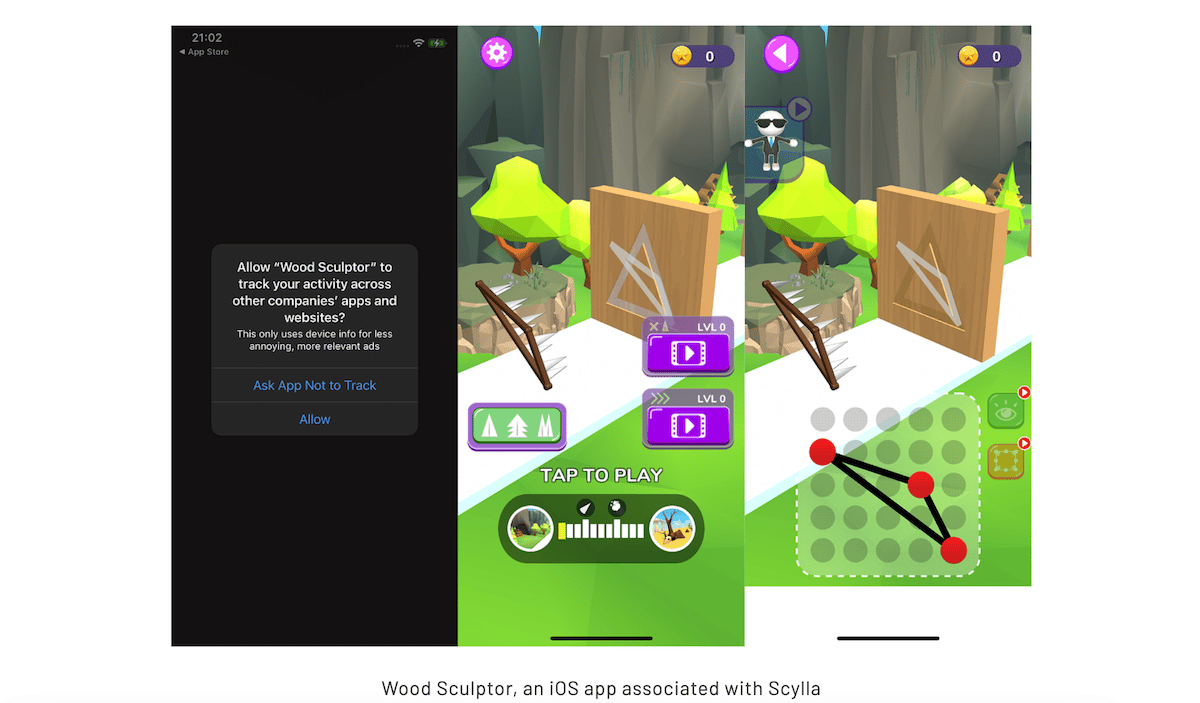
Downloaded millions of times, the Scylla apps use a bundle ID that does not match their publication name to misguide the advertising into believing that the ad clicks or impressions come for “more profitable” or legitimate apps.
Using the Job Scheduler system, the adware commences ad impression events when the devices are not in use like when the screen is off to avoid rising users’ suspicions.
HUMAN’s researchers found that 29 Scylla apps imitated up to 6,000 CTV-based apps and regularly cycled through the IDs to evade fraud detection.
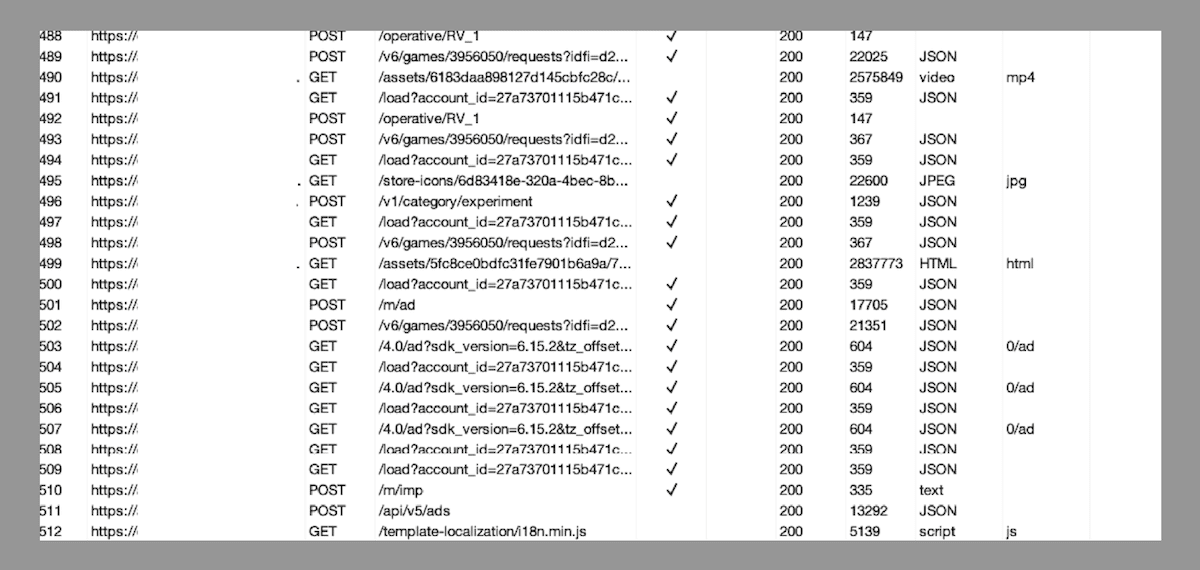
Researchers detailed that the new Scylla apps have additional layers of code obfuscation using the Allatori Java obfuscator which makes it difficult for researchers to detect and reverse engineer malware.
Here is a list of the most downloaded Adware on iOS, users are advised to monitor apps to filter out malware. A usual tell of such apps is rapid battery drain or increase in internet data usage. The complete list of Adware is available here.
- Loot the Castle – com.loot.rcastle.fight.battle (id1602634568)
- Run Bridge – com.run.bridge.race (id1584737005)
- Shinning Gun – com.shinning.gun.ios (id1588037078)
- Racing Legend 3D – com.racing.legend.like (id1589579456)
- Rope Runner – com.rope.runner.family (id1614987707)
- Wood Sculptor – com.wood.sculptor.cutter (id1603211466)
- Fire-Wall – com.fire.wall.poptit (id1540542924)
- Ninja Critical Hit – wger.ninjacriticalhit.ios (id1514055403)
- Tony Runs – com.TonyRuns.game