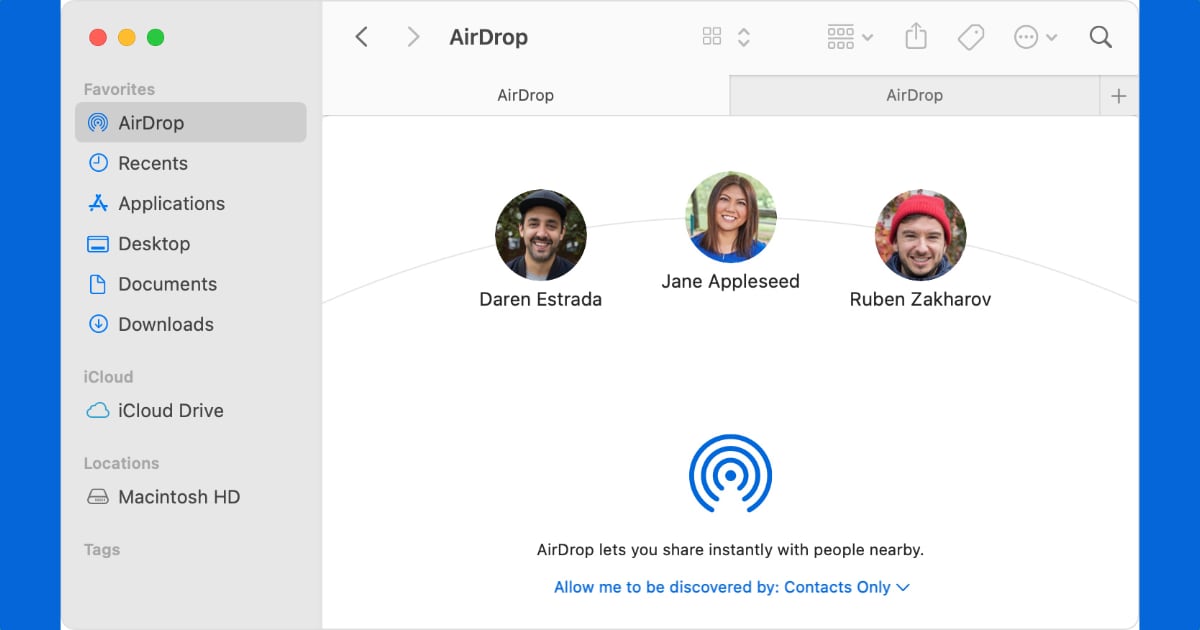
AirDrop for macOS and iOS allows Apple devices to easily share links and files with other Apple devices, without any complicated connection process. It seems that its ease of use also leads to a security flaw, as discovered by researchers at TU Darmstadt, which lets it share personal data like email addresses and phone numbers with strangers.
AirDrop shares phone number and email with strangers
Researchers from TU Darmstadt write in a new study that AirDrop defaults to sharing files with only contacts that are in a user’s address book. AirDrop uses phone numbers and email addresses for a mutual authentication mechanism that compares the phone number and email address with entries in the contact’s address book. If both are confirmed as each other’s contacts, file sharing can be initiated.
However, an attacker with a Wi-Fi-connected device and close proximity to the target can initiate the discovery process, simply by opening the sharing menu on an iPhone, iPad, or Mac.
As an attacker, it is possible to learn the phone numbers and email addresses of AirDrop users – even as a complete stranger. All they require is a Wi-Fi-capable device and physical proximity to a target that initiates the discovery process by opening the sharing pane on an iOS or macOS device.
Once the discovery process is initiated, hackers can bypass Apple’s method of hiding phone numbers and email addresses by using common methods such as brute force. The researchers say that users should disable AirDrop discovery in system settings to protect personal information.
The discovered problems are rooted in Apple’s use of hash functions for “obfuscating” the exchanged phone numbers and email addresses during the discovery process. However, researchers from TU Darmstadt already showed that hashing fails to provide privacy-preserving contact discovery as so-called hash values can be quickly reversed using simple techniques such as brute-force attacks.
In simple terms, it can be potentially easy for a hacker to gain phone numbers and email addresses, but it is important to note that no proof of concept or demonstration has been shared as part of this discovery. The researchers are expected to share their results in a scientific paper in August at the USENIX Security Symposium.
At the time of writing, Apple has not acknowledged or commented on this security flaw.



