A newly documented iPhone exploit framework called Coruna is drawing attention from security researchers after it was found to contain one of the most extensive collections of iOS exploits publicly documented. The toolkit targets iPhones running iOS 13 through iOS 17.2.1 and bundles 23 separate exploits designed to break into devices through infected websites.
Researchers at Google’s Threat Intelligence Group first identified the framework in early 2025. Since then, it appears to have circulated among multiple threat actors, moving from a commercial surveillance customer to a suspected Russian espionage campaign and later to financially motivated cybercriminals operating from China. The discovery highlights how sophisticated exploit frameworks can move between different groups, effectively creating a secondary market for previously undisclosed vulnerabilities.
The Coruna iOS exploit kit is built around five full exploit chains that automatically adapt to the device they are targeting. When a user visits a compromised website, the framework fingerprints the iPhone to determine its exact model and iOS version. It then selects the correct exploit for that configuration, allowing attackers to target multiple generations of iOS devices with a single toolkit.
The attacks rely heavily on WebKit vulnerabilities and related privilege escalation techniques. One example includes CVE-2024-23222, a type confusion bug in WebKit that Apple patched in iOS 17.3 and iPadOS 17.3. Earlier flaws used in the exploit kit affect versions of iOS dating back to 2020, demonstrating how older unpatched devices remain attractive targets for attackers.
Coruna is also engineered with strong anti analysis techniques. Its code is encrypted and packaged in a custom format designed to make reverse engineering difficult. Researchers also discovered that the exploit framework includes internal documentation written in English and uses several exploitation techniques that have not previously been observed publicly.
The payload delivered after a successful exploit focuses heavily on financial theft. According to researchers, the malware can interact with at least 18 different cryptocurrency applications to extract wallet credentials. It also scans files on the device for QR codes that may contain wallet information and searches for BIP39 seed phrases or keywords such as backup phrase and bank account.
Another notable capability is its ability to scan the Apple Notes app for recovery phrases commonly used to restore crypto wallets. Combined with QR code decoding and credential extraction modules, the toolkit appears specifically designed to target digital asset holders and financial information stored on a device.
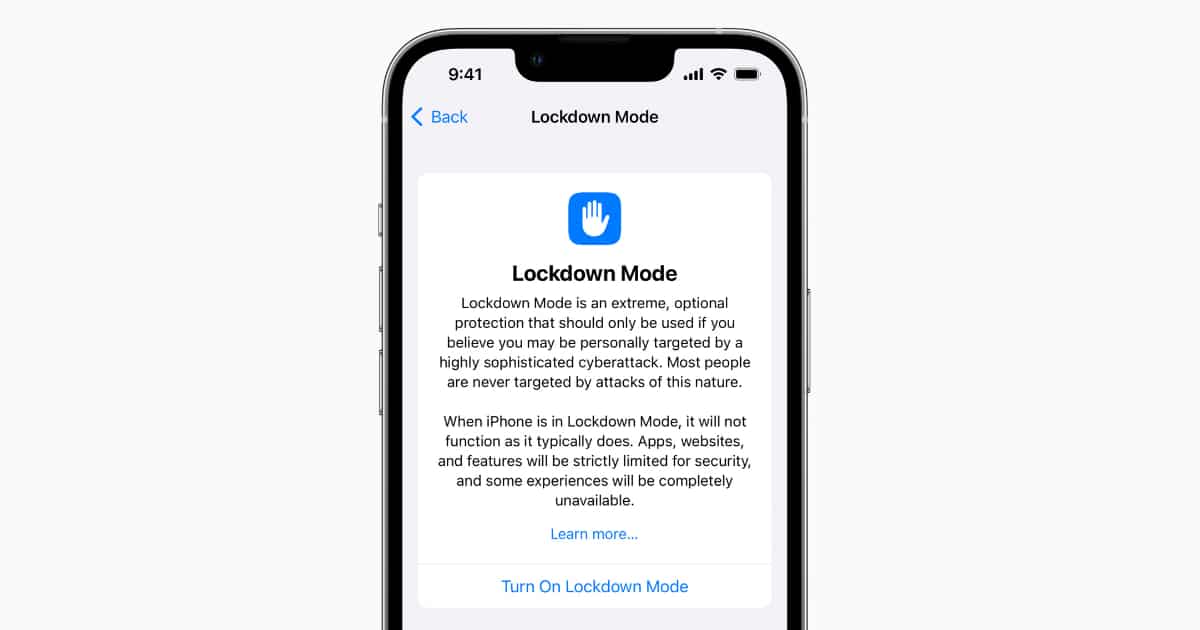
Despite its sophistication, the exploit kit has a clear limitation. If an iPhone has Apple’s Lockdown Mode enabled, the framework immediately aborts the attack and does not attempt exploitation. Lockdown Mode significantly restricts several system functions including web content processing, which makes many of these advanced attacks far more difficult to execute.
The exploit kit also fails on newer versions of iOS. Devices running versions newer than iOS 17.2.1 are not vulnerable to the exploit chains identified in the report because the relevant security bugs have already been patched.
For users, the main takeaway is straightforward. Keeping an iPhone updated to the latest version of iOS remains the most effective defense against these types of attacks. Enabling Lockdown Mode provides an additional layer of protection for individuals who may be at higher risk, such as journalists, activists, and researchers.


