After the cellphone hacking company, Cellebrite revealed it had figured out a way to access the secure messaging app Signal, the founder of the encrypted chat app responded by obtaining Cellebrite’s hacking kit and discovered several vulnerabilities. Signal founder Moxie Marlinspike also implied that the messaging app will be updated to thwart any law enforcement attempts to hack it.

Signal CEO reveals how easy it is to hack Cellebrite, a phone-hacking tool used by police
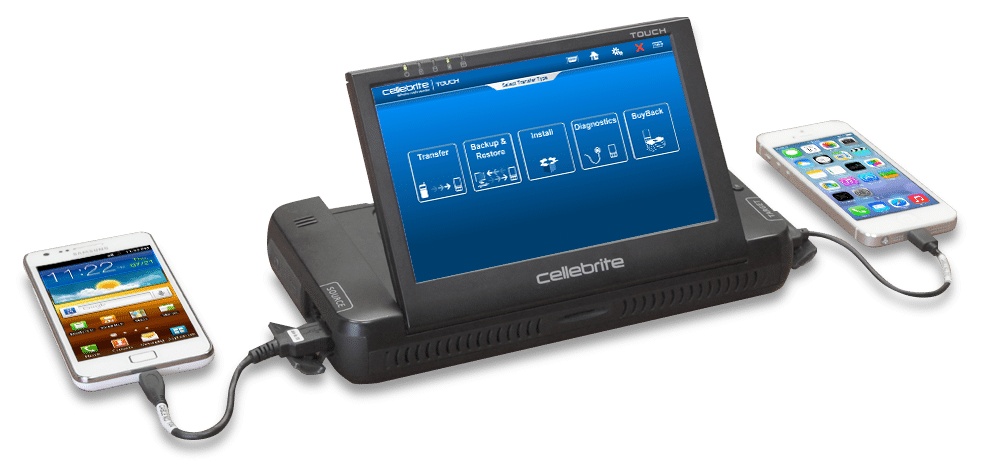
Cellebrite sells a number of “data analysis devices” called UFED that enable law enforcement to break into iOS or Android devices and obtain extract messaging logs, call records, photos and, other data. The suit of hacking tools has reportedly been used by the FBI to unlock iPhone in the past – something Apple has spoken out against in defense of user privacy.
In a blog post on Wednesday, Signal founder Moxie Marlinspike reported several vulnerabilities in Cellebrite’s hacking hardware that could be used to run malicious code on a machine used to analyze an unlocked device. That would most likely be a police or government investigator’s machine.
Marlinspike went on to explain that there are “virtually no limits” on the type of malicious code that could be executed using the vulnerabilities.
“For example, by including a specially formatted but otherwise innocuous file in an app on a device that is then scanned by Cellebrite, it’s possible to execute code that modifies not just the Cellebrite report being created in that scan, but also all previous and future generated Cellebrite reports from all previously scanned devices and all future scanned devices in any arbitrary way (inserting or removing text, email, photos, contacts, files, or any other data), with no detectable timestamp changes or checksum failures. This could even be done at random, and would seriously call the data integrity of Cellebrite’s reports into question.”
The blog post also contains a video demonstrating an iPhone tricking Cellebrite’s UFED device to post a hacker-created message using the vulnerabilities present on the device. The founder of the app also implied that Signal is adding some specially formatted files to its code that are capable of scrambling Cellebrite’s technology.
Read Also:




1 comment