David Shayer, a former Apple engineer who was familiar with the project claims that a secret iPod was built in 2005 by engineers from the U.S Department of Energy with assistance from Apple’s engineers. The 5th generation iPod, with an easy-to-open case and large 60 GB disk, was modified for the project but for an unknown purpose.
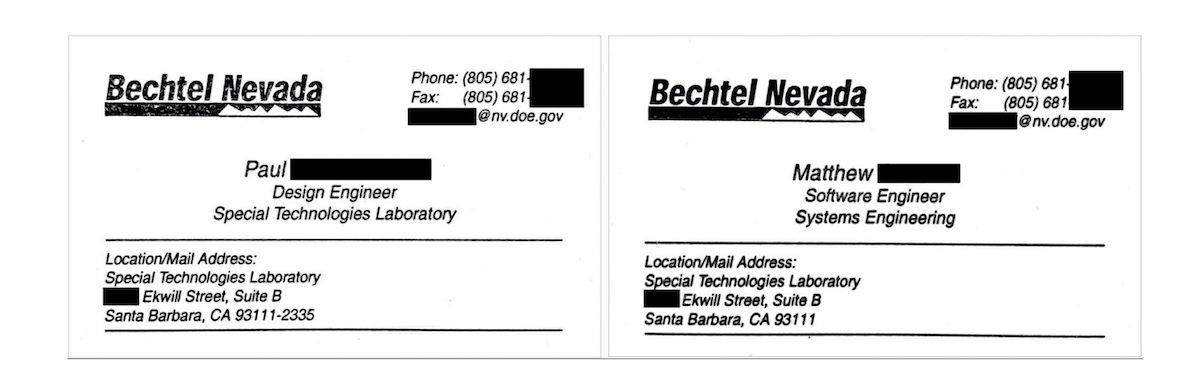
In an interview with TidBits, Shayer recalled the day when he was assigned this secret project by his “boss’s boss” and introduced to special agents to provide “any help they needed from Apple.” According to him, the agents were did not work for the US Department of Energy, instead were from Bechtel which is a large U.S defense contractor for the Department of Energy.
He told that only members of the top management knew about the project, which was even kept a secret from his line manager. Shayer said,
“I learned that an official at the Department of Energy had contacted Apple’s senior vice president of Hardware, requesting the company’s help in making custom modified iPods. The senior VP passed the request down to the vice president of the iPod Division, who delegated it to the director of iPod Software, who came to see me. My boss was told I was working on a special project and not to ask questions.”
Building the Top Secret iPod
Shayer was chosen to assist agent Paul and Matthew on this top-secret project because he wrote the iPod’s file system, the SQLite database which tracked all the songs on the device and eventually worked on every part of the iPod software except the audio codecs to convert MP3 and AAC files into audio. While the government agents did all the work, his job “was to get Paul and Matthew up and running on a new operating system they’d never seen before, much less developed for.”
Apple’s role in the building this special iPod was purely advisory, Shayer makes it clear that at any stage of the process, the company did not provide any help in the physical build of the device.
“This wasn’t a collaboration with Bechtel with a contract and payment; it was Apple doing a favor under the table for the Department of Energy. But access for that favor went only so far.
Needless to say, Paul and Matthew weren’t allowed to access our source code server directly. Instead, I gave them a copy of the current source code on a DVD and explained it couldn’t leave the building. Ultimately, they were allowed to keep the modified copy of the iPod OS they built, but not the source code for it.
Apple didn’t provide them any hardware or software tools. I gave them the specs for the Windows computers they needed, along with the ARM compiler and JTAG debugger. They bought retail iPods to work on, several dozen at least, possibly many more.”
Was the iPod Modified to Spy?
All the communication and dealing, related to this project, were in person. Thus, there is no paper trail of evidence that it ever happened. Shayer, the director of iPod Software, the vice president of the iPod Division, and the senior vice president of Hardware were the only people aware of it and now none of them works at Apple.
Since the agents were working for the Department of Energy which is responsible for US nuclear weapons and nuclear power programs, Shayer believes that they modifying the iPod to be used as a stealth Geiger counter, secretly. A deceptive device to listen to music ostentatiously but mainly used to record radioactivity, scan for uranium (smuggled or stolen), track evidence of secret bomb development program without attracting media’s attention.
Although Paul and Matthew never disclosed what they were working, the Fiscal year 2005 budget of the Department of Energy supports Shayer theory. In 2005 the Department allotted $9 billion for defense-related objectives.
“The budget request maintains commitments to the nuclear deterrence requirements of the Administration’s Nuclear Posture Review and continues to fund an aggressive strategy to mitigate the threat of weapons of mass destruction.”
Personally, this story feels like it is out a James Bond movie in which super-smart individuals build secret weapons or tracking devices as normal gadgets to deceive the normal eye. Shayer’s recount of the whole process gave me goosebumps and got me thinking of what happens behind billion dollars walls. For me, this story shades Apple’s claims of transparency, what are your thoughts?
Read Also:

