iPhone, iPad, and Mac are protected with biometric authentication systems like fingerprint scan and face recognition to prevent unauthorized access to their private information. Apple wants to expand the same security to AirPods as well. A new patent granted to Apple by the U.S. Patent and Trademark Office describes an authentication system for users’ identification using headphones.

This is not the first patent that suggests that Apple wants to improve AirPods capabilities. Recently, the tech giant was granted a patent “Optical audio transmission from source device to wireless earphones” for the use of an optical cable to improve Bluetooth bandwidth on AirPods or Bluetooth headphones to improve communication between devices.
To prevent unauthorized access to users’ personal devices, AirPods might be equipped with authentication technology
The filing explains that through the use of headphones paired with an Apple device, an unauthorized person can gain access to someone’s private information. Therefore, a users verification system in the headphones can prevent such incidents.
Headphones, such as headphones communicatively coupled to an electronic device, can provide a useful interface between human users and electronic devices. In general, headphones may be utilized for listening to audio from another device and performing other various functions, such as providing voice commands to the device via the headphones.
For example, a user may provide a speech input containing a user request to a digital assistant operating on an electronic device such as a mobile device. The digital assistant can interpret the user’s intent from the speech input and operationalize the user’s intent into tasks.
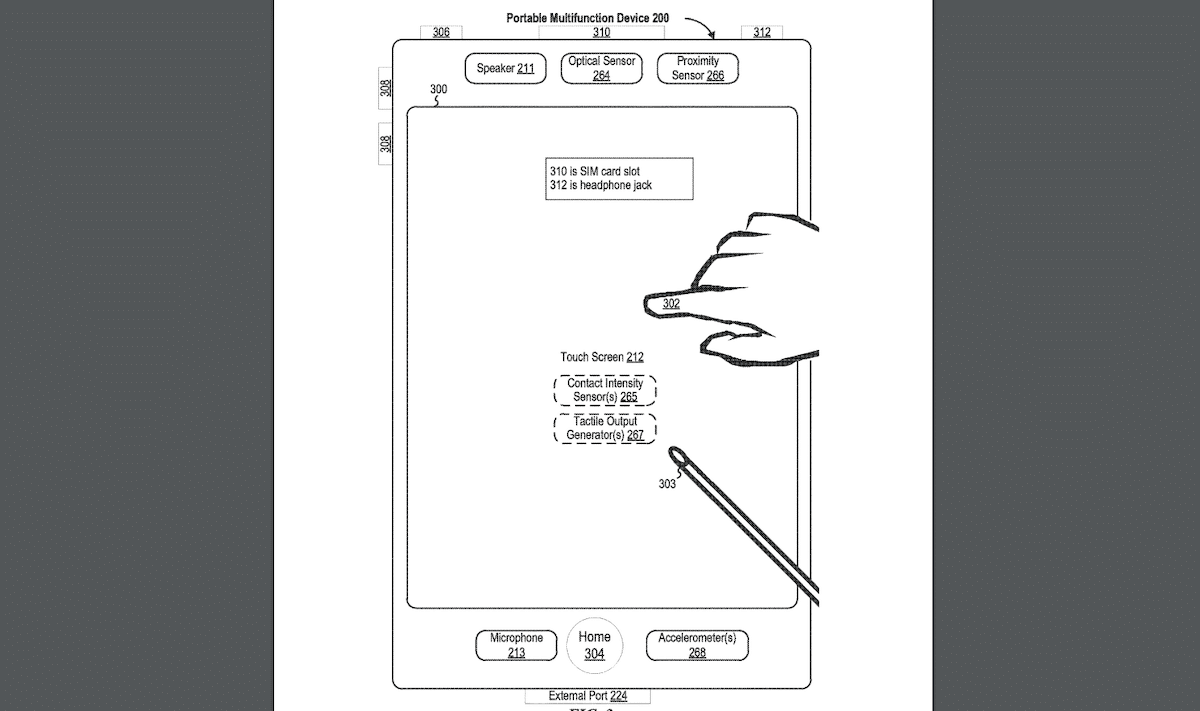
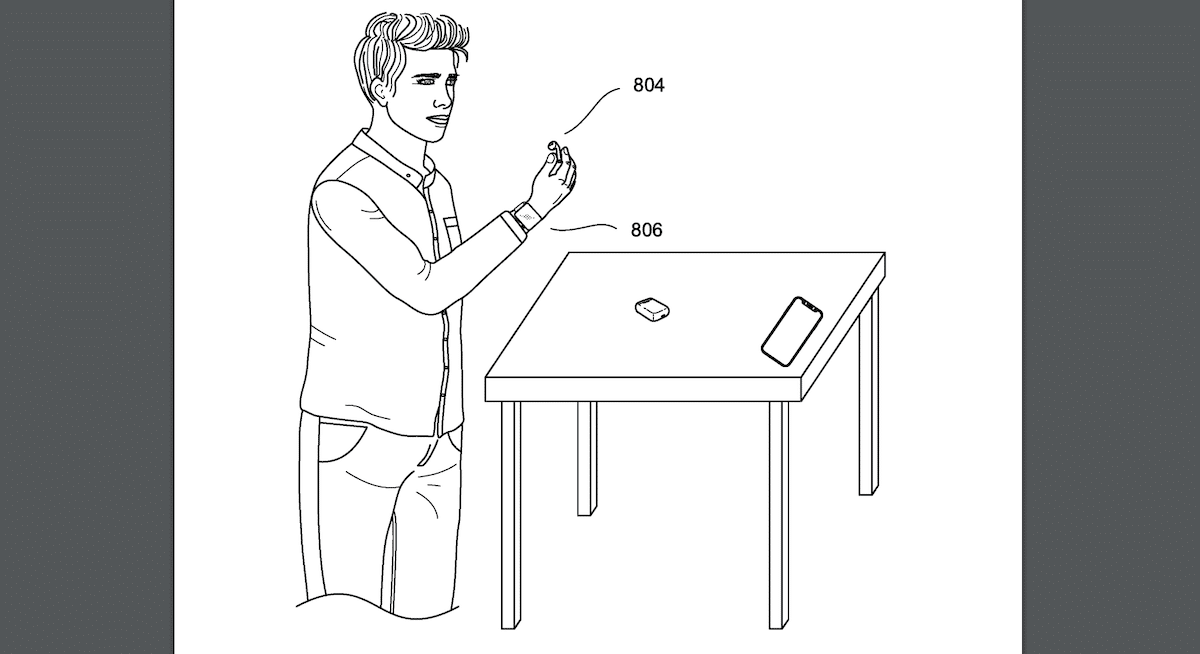
The company is exploring users verification via different technologies. One way for authentication is through recognizing users’ set behavior patterns of movement registered on their iPhone, Apple Watch, and AirPods like the pattern of tapping the screen.
Systems and processes for user identification using headphones associated with a first device (e.g., a smartphone) are provided. For example, first movement information corresponding to movement of a second electronic device (e.g., a headphone) is detected. Second movement information corresponding to movement of a third electronic device (e.g., a smartwatch) is detected. A similarity score is determined based on the first movement information and the second movement information. In accordance with a determination that the similarity score is above a threshold similarity score, a user is identified as an authorized user of the first electronic device and the second electronic device. Based on the identification, an output is provided to the second electronic device.
The second method for authentication is the use of use ultrasonic signals, like a sonar, to detect the shape of the users’ ear canal.
For example, various characteristics of the user’s ear provide an echo of the ultrasonic signal which is unique to the user. Variations in the surface of the user’s ear canal may cause the ultrasonic signal to reflect off the surface and generate an echo having a signature that is associated with the user.
Currently, a device has to be unlocked for anyone to gain access to the owners’ data or command Siri to read their messages. The aforementioned scenarios are assuming access to unlocked devices.
Read More:



