A recently published patent by the U.S Patent and Trademark Office reveals that Apple is working on a new capability to allow multiple users to use a single device without compromising their personal information. According to the document, Apple had filed for ‘Provision of domains in secure enclave to support multiple users’ on December 6, 2017, and now it has been approved by the regulatory body.
The filing details the system, method, and apparatus to set up different domains in a “secure enclave processor” to enable multiple users to log in on a device. The functionality works like multiple users access on a Mac with different accounts, however, the new system will be more secure by blocking access to any data stored in an “unencrypted manner.”
Apple working on multiple users log in on devices
Apple’s developers explain that users save their data on devices by setting a passcode or password on a login screen but at times it is possible for hackers to access stored data without knowledge of the authentication password or passcode and can extract data from memory “if the data is stored in an unencrypted manner.” If the hacker has physical possession of the device, he/she can remove the storage devices and access them by a different system.
Computing device passcodes can be used to enable data encryption by providing entropy to an encryption algorithm that enables the generation of one or more per-user keys that may then be used secure data within the computing system. The per-user keys can be combined with system or group keys to provide enable multi-layer encryption of data and encryption keys to defend against data that is accessed outside of the normal login process, for example, via physical access to a storage device.
Notwithstanding various data protection techniques implemented in computing systems known in the art, cryptographic and cryptanalysis techniques continuously evolve. Accordingly, updated techniques of computing device security are regularly developed.
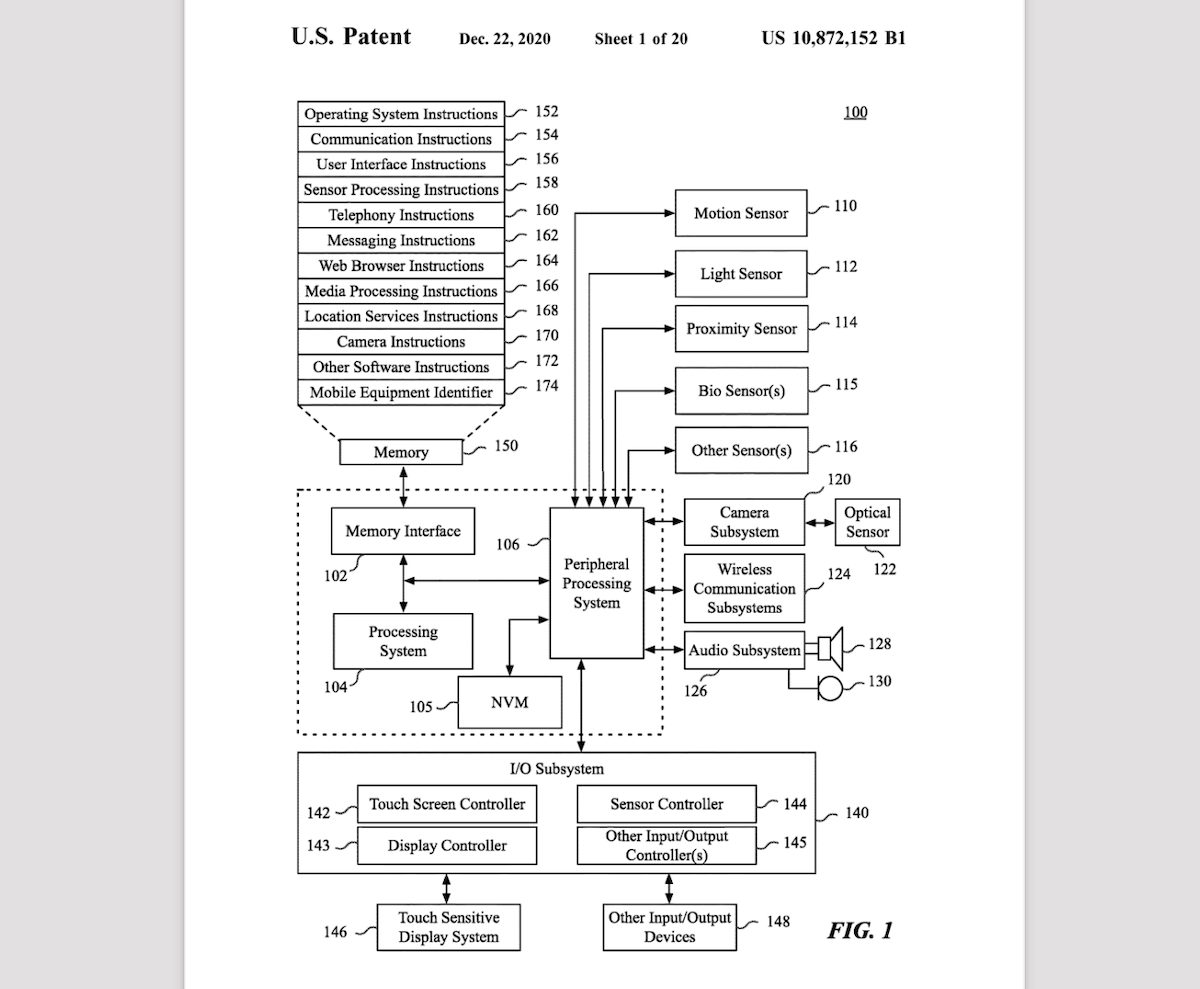
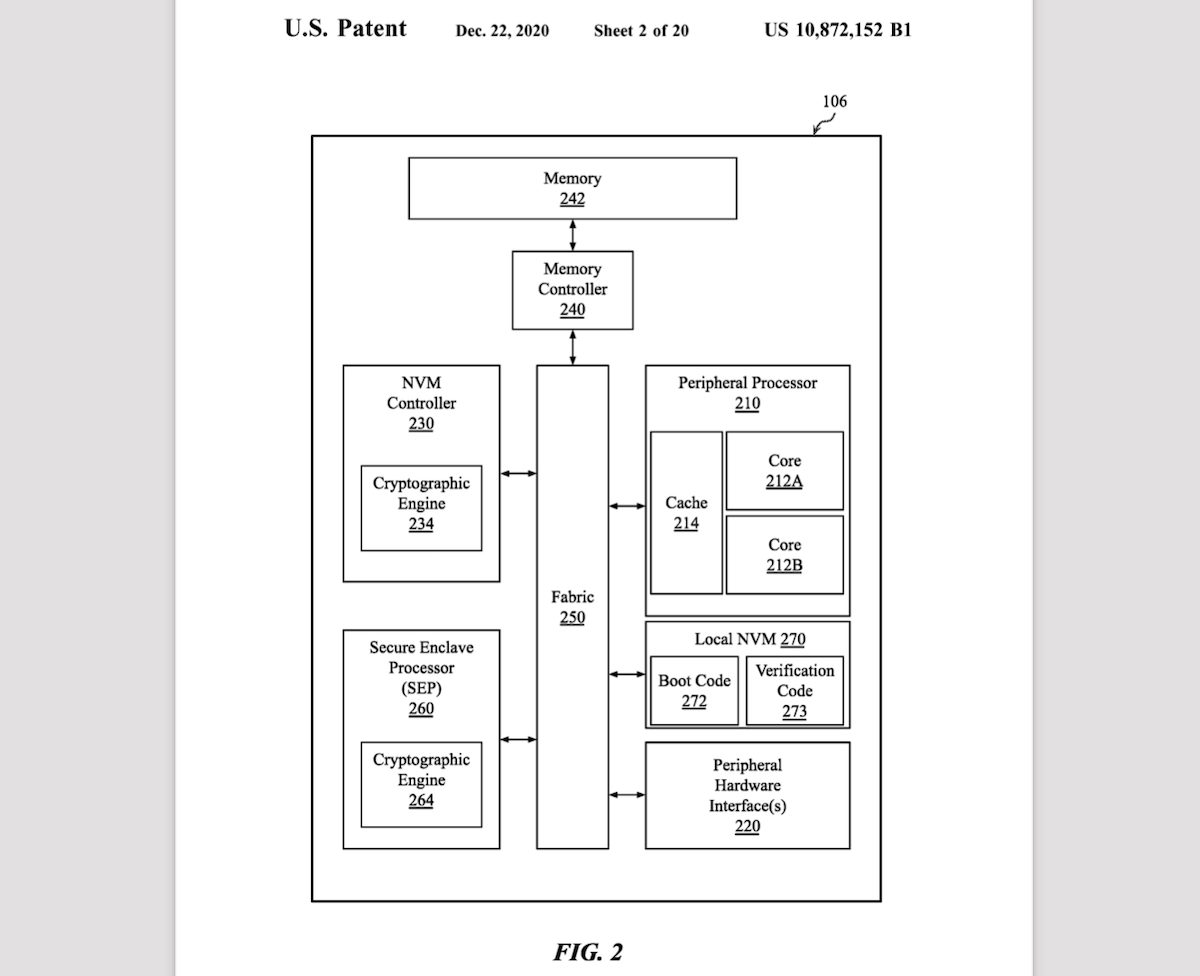
Therefore, the filing describes a new more secure system with two processors.
One embodiment provides for an apparatus comprising a first processor to receive a set of credentials associated with one of multiple user accounts on the apparatus and a second processor including a secure circuit to provide a secure enclave, the secure enclave to receive a request from the first processor to authenticate the set of credentials, the request including supplied credentials and an authentication type, where the secure enclave is to block the request from the first processor in response to a determination that the user account has exceeded a threshold number of successive failed authentication attempts for the authentication type.
Read More: