A proof-of-concept website reveals that a design flaw of iOS 16 “Lockdown Mode” allows websites to identify users who have enabled the feature. Although the Lockdown Mode will ensure users’ security, it will jeopardize their privacy.
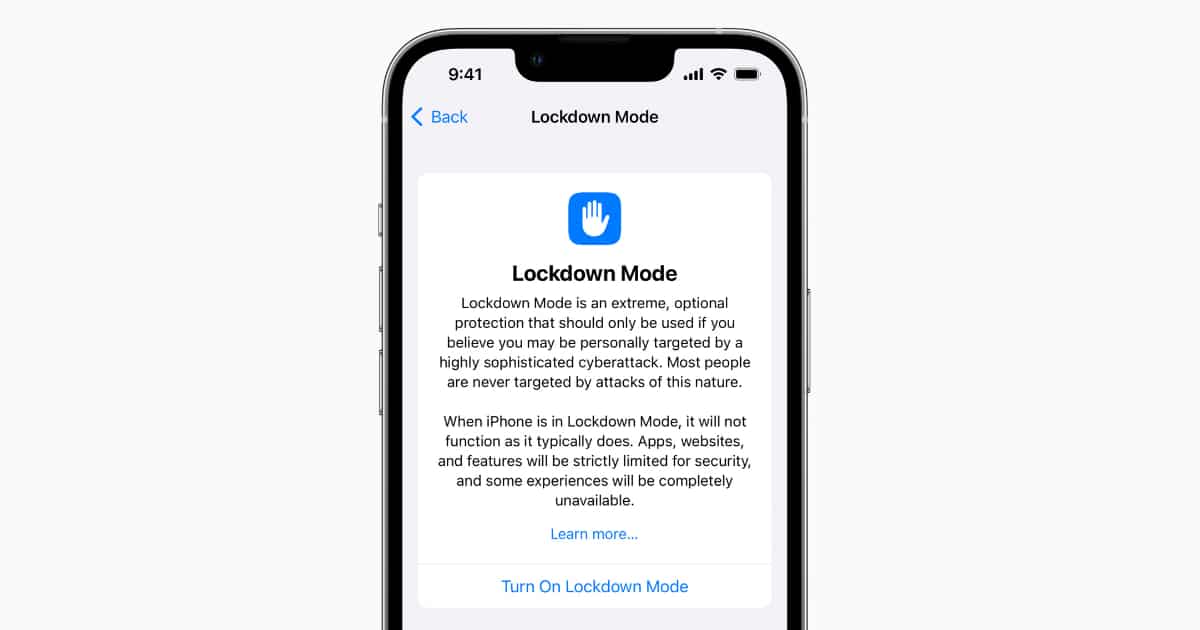
To protect users who are targets of sophisticated spyware like government officials, journalists, and human rights activists, Apple has introduced the “Lockdown Mode” in the upcoming iOS 16, iPadOS 16, and macOS Ventura updates. Called the “extreme” mode of protection, the feature will activate certain functionalities when enabled like disabling images and links in the Messages app, JavaScript compilation, Apple services, and others.
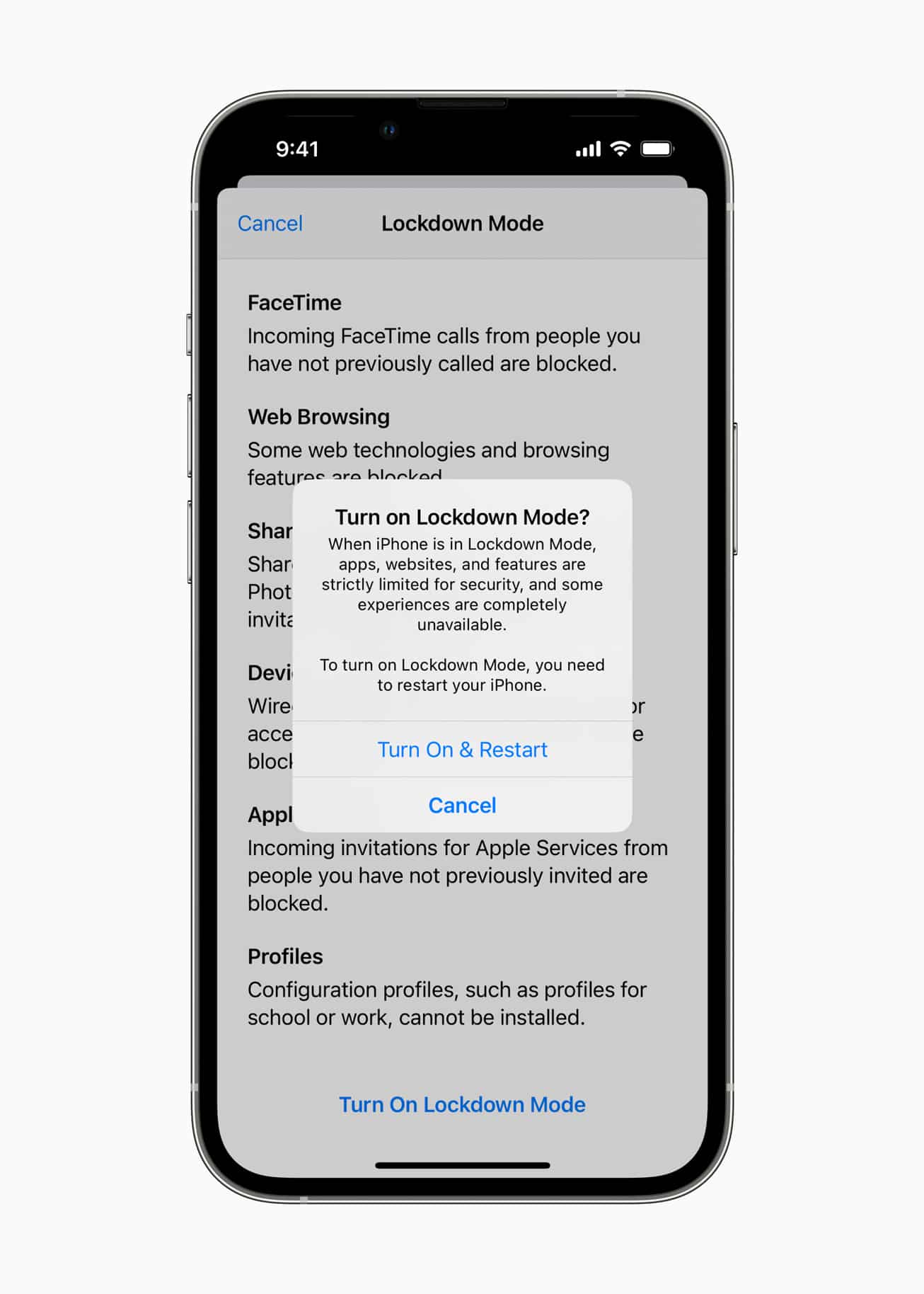
Lockdown Mode disables a series of features that enable websites to fingerprint users
A privacy-focused company, Cryptee created a proof of concept website that detects if a user has the Lockdown Mode feature turned on or off. CEO of the company and a privacy activist, John Ozbay explained to Motherboard that the new privacy mode disables certain features like custom fonts which enables websites to fingerprint users who opt in the mode.
“Let’s say you’re in China, and you’re using Lockdown Mode. Now, any website that you visit could effectively detect you are using Lockdown Mode, they have your IP address as well. So they will actually be able to identify that the user with this IP address is using Lockdown Mode,” Ozbay said in a call. “It’s a tradeoff between security and privacy. [Apple] chose security.”
Ozbay also said that it was very easy for them to detect the users who had enabled the feature because it is a design flaw and not a bug. An Apple employee also corroborated Cryptee’s finding.
“web fonts are disabled intentionally to remove font parsing from available web attack surface,” and that “watering hole attacks are part of our threat model, so I’m not sure it would make sense to have web font exceptions per site.” (Watering hole attacks are exploits where hackers lure a victim to a known website where they injected malware, or a copycat of a known website that serves malware.)
The report concludes that fingerprinting users and finding their IP addresses through the new mode is equivalent to painting a massive target on the user’s backs who are most vulnerable, and the only way to limit users’ visibility online would be if everyone enables the Lockdown Mode and blends in the crowd.
“As for fingerprinting, it’s sadly a trade off we always have to deal with. The same is true of Tor and the Tor Browser—they go to huge lengths to reduce any fingerprinting ability but you end up standing out because you’re the one with less traceable fingerprints,” Ryan Stortz, an independent security researcher who has studied iOS, told Motherboard.



