In 2018, Apple introduced a T2 security chip for Macs which prevents hackers from altering macOS to gain access to users’ computers. However, Passware, a company that sells password cracking tools claims that it has found a T2 Mac security flaw to decipher users’ login passwords to gain access to the locked machines.
“The Apple T2 Security Chip is Apple’s second-generation, custom silicon for Mac. The T2 chip delivers capabilities to your Mac, such as encrypted storage and secure boot capabilities, enhanced image signal processing, and security for Touch ID data.”
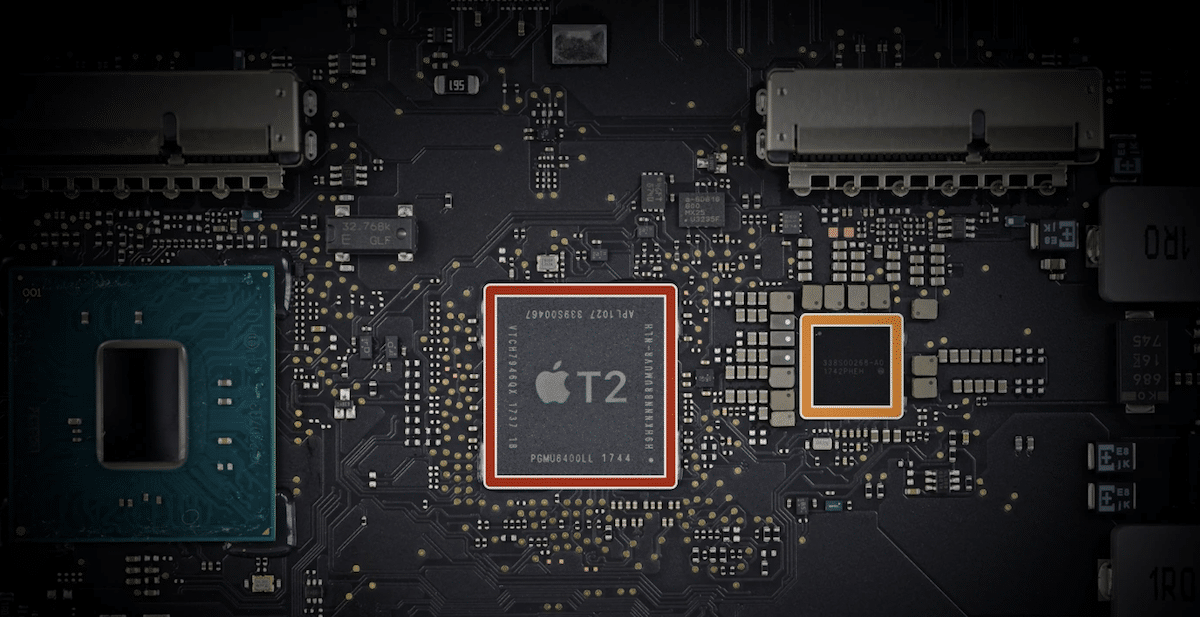
Exploiting a T2 Mac security flaw, Passware can crack a 6-digit password in 10 hours via brute-force attacks
Brute-force attacks inject multiple guesses/ variations of a password in seconds to hack into locked Macs or Windows PCs. However, Macs with T2 chips block brute-force attacks because the system locks the user out after a few wrong password attempts. 9to5Mac writes that:
Until recently, however, it wasn’t practical to mount brute-force attacks on Macs with a T2 chip. This is because the Mac password is not stored on the SSD, and the chip limits the number of password attempts that can be made, so you’d instead have to brute-force the decryption key, and that is so long it would take millions of years.

Now, Passware says that it offers an add-on module that can crack Macs login passwords by breaching the T2 chip’s security which prevents multiple guesses and provides a dictionary of 550,000 most commonly-used passwords to try up to 15 passwords in a second. Although it is a slow process, it can crack a conventional 6 digit in 10 hours. The company says that its password cracking tool is for government clients and private companies with a valid justification for its use.
Having defeated this protection, users can then apply the dictionary of their choice. Passware provides a dictionary of the 550,000 most commonly-used passwords (created from various data breaches), along with a larger one of 10 billion passwords.
The process is still slower than usual, at a relatively sedate 15-ish passwords per second. In theory, this could still take thousands of years, but most people use relatively short passwords which are vulnerable to dictionary attacks. The average password length is just six characters, which can be cracked in around 10 hours.
Now, several websites advise users to keep longer passwords with capital and lower case alphabets, numbers, and special characters like !@$%^&*. But some users who find it difficult to memorize or keep track of different passwords, prefer to keep easy-to-remember passwords which makes them vulnerable to such attacks.
Recently, the use of iPhone spyware like Pegasus, and Predator was highlighted to hack into iPhones running on the latest iOS 14 and later versions which raised concerns about iOS security, and now Macs security is also vulnerable to brute-force attacks.