Apple claims its iPhone is one of the safest devices in the world. A new report by The Citizen Lab says otherwise. After bringing the use of Pegasus spyware by NSO to hack iPhones by suppressive regimes, the researchers highlight the use of another spyware, Predator by Cytrox, to breach iPhone’s security.
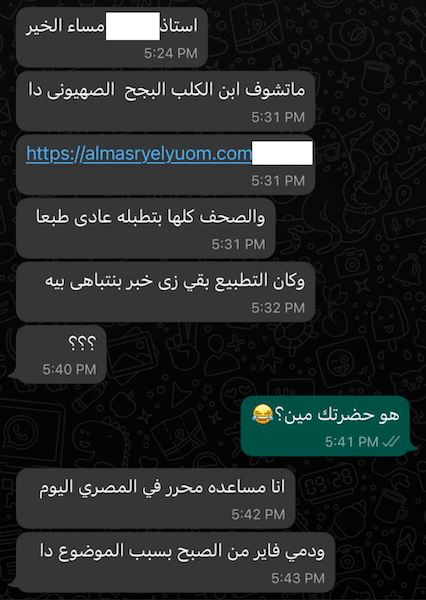
In June 2021, iPhones of two Egyptians living in exile became targets of cyber attacks by Pegasus and Predator: Politician Ayman Nour living in Turkey is a strong critic of President Abdel Fattah el-Sisi who took over the country after the 2013 military coup and a host of popular news program who wished to stay anonymous.
Pegasus and Predator spyware infected the victim’s iPhones concurrently
Cytrox is a North Macedonia-based spyware developer which for the first time has been documented for targeting iOS and Android smartphones. Unlike the known zero-day exploit used by Pegasus, Cytrox’s spyware used a new single-click exploit sent via WhatsApp to access the victim’s camera, microphone, and phones’ data. More importantly, the spyware creates automation suing the Shortcuts feature on iOS to survive in the system, even after a reboot which typically removed such threats.
The research found that iPhones of both victims were running on iOS 14.6 and spyware used new exploits to breach their security. Upon conducting the internet scan for the Predator server, it was found that its customers are in Armenia, Egypt, Greece, Indonesia, Madagascar, Oman, Saudi Arabia, and Serbia.
The phone of Ayman Nour was simultaneously infected with both Cytrox’s Predator and NSO Group’s Pegasus spyware, operated by two different government clients.
Bill Marczak, Citizen Lab researcher who discovered and analyzed the Predator malware said, “based on the slapdash nature of Predator’s code, it’s clear we’re looking at the B Team here. Even so, Predator was still able to break into the latest, fully up-to-date phones, so it’s no surprise that we found repressive governments, including Egypt and Saudi Arabia, as Predator operators.”
The spyware-for-hire industry is bigger than perceived. Unlike NSO which is under scrutiny for attacking unsuspecting citizens, others like Cytrox have been operating under the radar fearlessly with impunity.
This report is the first investigation to discover Cytrox’s mercenary spyware being abused to target civil society. Remarkably, one of the victims was simultaneously infected with NSO Group’s Pegasus spyware. NSO Group has received outsized publicity in recent years, thanks to a growing customer list, spiraling abuse problems, and groundbreaking investigative work by civil society. Cytrox and its Predator spyware, meanwhile, are relatively unknown.
Cytrox was reported to be part of Intellexa, the so-called “Star Alliance of spyware,” which was formed to compete with NSO Group, and which describes itself as “EU-based and regulated, with six sites and R&D labs throughout Europe.”
Following the iPhone hacking report, Meta banned Cytrox from its platform
Meta, former Facebook, has been the first company to take action against the global “Surveillance-For-Hire” industry which is used by suppressive governments to target people by compromising their devices across the internet. It not only conducted an investigation on these “cyber mercenaries” but also banned multiple outfits.
The “surveillance-for-hire” entities we removed violated multiple Community Standards and Terms of Service. Given the severity of their violations, we have banned them from our services. To help disrupt these activities, we blocked related internet infrastructure and issued Cease and Desist letters, putting them on notice that their targeting of people has no place on our platform. We also shared our findings with security researchers, other platforms, and policymakers so they can take appropriate action. See a full list of entities we took down in the Threat Report.
Recently, Apple sued NSO for and its parent company in the United States Federal Court, seeking a permanent injunction to ban the company from using Apple products, including its hardware and software. And the company sends “Threat Notifications” to inform possible targets of state-sponsored attacks.



