A group of security researchers detailed how they spent three months hacking Apple, uncovered various vulnerabilities in the company’s digital infrastructure and received bounty payments that add up to more than $50,000.
The Cupertino tech company retains a bug bounty program that pays security researchers for found weaknesses. As researcher Sam Curry notes, he previously thought that the tech company only paid bounties for problems concerning physical products like the iPhone.

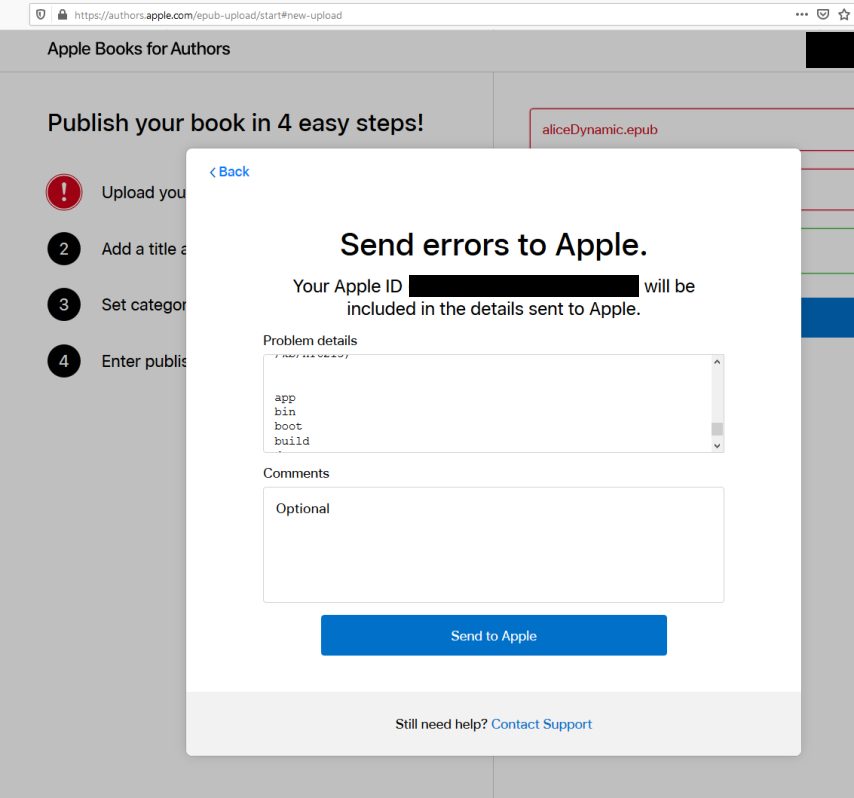
Hackers discover 55 Apple vulnerabilities
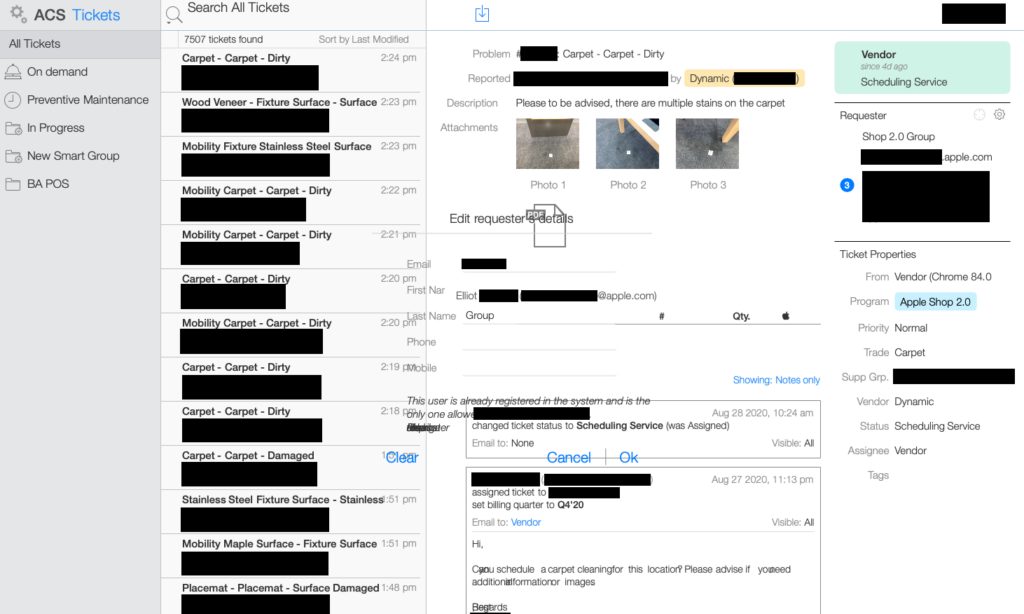
The group of security analysts: Sam Curry, Brett Buerhaus, Ben Sadeghipour, Samuel Erb, and Tanner Barnes, went though Apple’s infrastructure extensively over the course of three months. The group says they found 55 vulnerabilities of varying severity, 11 were critical and 29 high severity vulnerabilities. They also stated that the Cupertino tech company had addressed “the vast majority” of their findings, usually within one or two business days, and sometimes just a few hours. The report states,
“During our engagement, we found a variety of vulnerabilities in core portions of their infrastructure that would’ve allowed an attacker to fully compromise both customer and employee applications, launch a worm capable of automatically taking over a victim’s iCloud account, retrieve source code for internal Apple projects, fully compromise an industrial control warehouse software used by Apple, and take over the sessions of Apple employees with the capability of accessing management tools and sensitive resources.”
The team was driven to capitalize on the program after realizing that Apple’s Security Bounty Program extends beyond the tech giant’s physical products to their web assets and infrastructure too. Curry writes:
“This caught my attention as an interesting opportunity to investigate a new program that appeared to have a wide scope and fun functionality. At the time I had never worked on the Apple bug bounty program so I didn’t really have any idea what to expect but decided why not try my luck and see what I could find.”
As of October. 4, the team has received four bounty payments totaling $51,500 for some of the vulnerabilities and expects the tech company to send additional payments for even more critical flaws.
The report goes into extensive detail regarding various vulnerabilities and strategies around finding and attacking weaknesses. You can read the full report here.
The team’s work is indicative of the success Apple’s Security Bounty program has in helping researchers pin down problems in the tech giant’s ecosystem before they become issues for the wider population.
Read Also:




1 comment