Researchers at SOPHOS have unearthed a global cryptocurrency scam that preys on victims looking for love, hence the name ‘CryptoRom’ scam. Scammers use dating sites and apps to get acquainted with the victims and after building a rapport, push them to install fake cryptocurrency apps on iPhone via an ad-hoc App Store. This scam is still active and is targeting mostly iPhone users in Asia, Europe, and the U.S.
Last month, a similar scam was found at the time of Apple’s iPhone 13 launch event. Scammers created a fake YouTube stream of the event before it went live. The unsuspecting fans who stayed on the fake channel for long enough were shown a scam Bitcoin promotion from Apple to double their money. It was estimated that the scammer stole $69,000 in a short time.
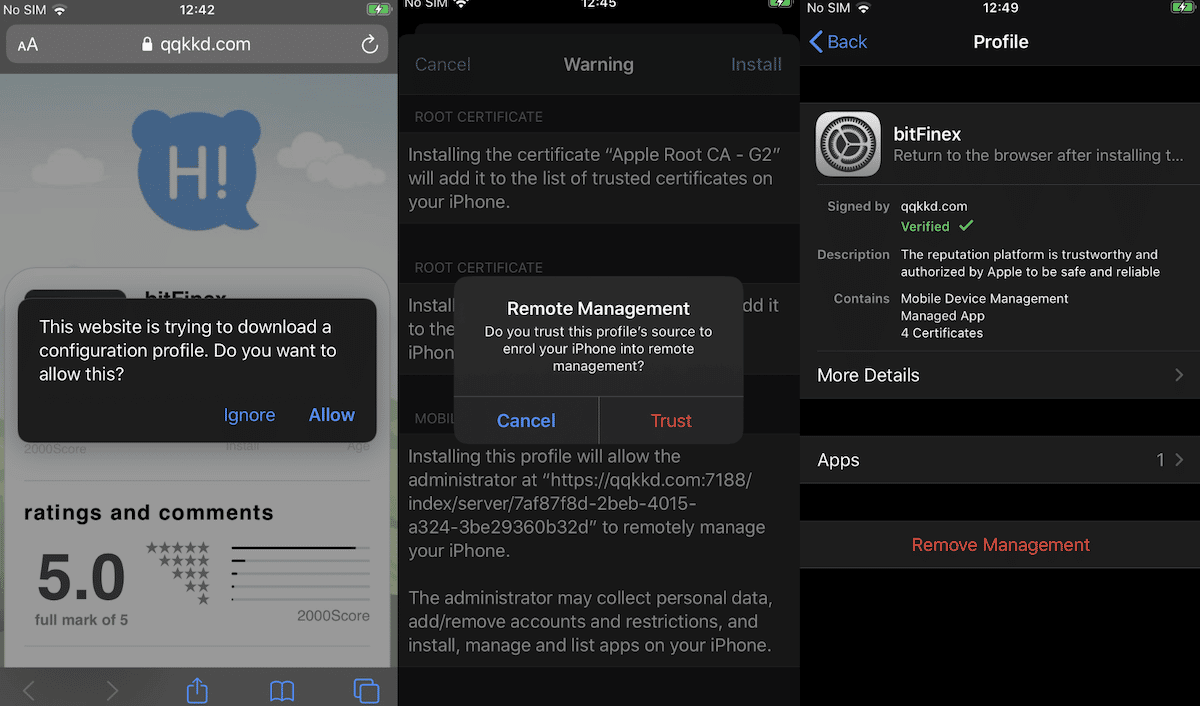
CyrptoRom scammers use Apple’s Enterprise Signature distribution scheme to let victims download fake apps outside the App Store
It was found that scammers used Apple’s ad hoc distribution method via “Super Signature services” and also that the malware abused the company’s Enterprise Signature distribution scheme to target victims.
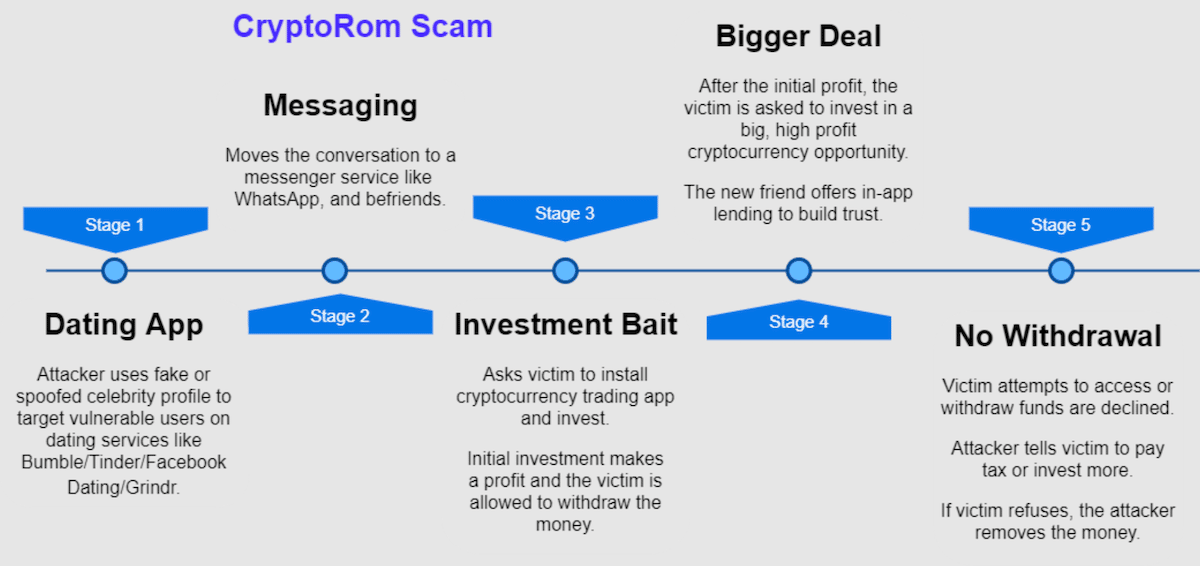
The modus operandi of the attackers is that they patiently lure victims in by faking a romantic connection on dating sites and apps like Tinder, Facebook dating, Bumble, and Grindr and later move on to messaging apps. After earning the victims’ trust, the attacker asks them to download trading apps that look authentic with a domain and customer support. Next, the victims are asked to invest a small amount which can be withdrawn with a little profit to build more trust. Once the victims invest larger sums of money and purchase financial products, they can not withdraw their money and eventually get locked out of the account.
So far, Interpol and victims have reported losing thousands of dollars and pounds.
From news reports, we learned one victim lost £63000 (~ $87000). There are additional news reports in UK of these scams, with one victim losing £35000 (~$45000) to a scammer who contacted them through Facebook, and another who lost £20000($25000) after being scammed by someone who contacted through Grindr.
In the latter case, the victim made an initial deposit, transferred money to a Binance application from their bank and then to crooks; they were then asked to deposit more funds in order to withdraw their money. None of these victims have gotten their money back.
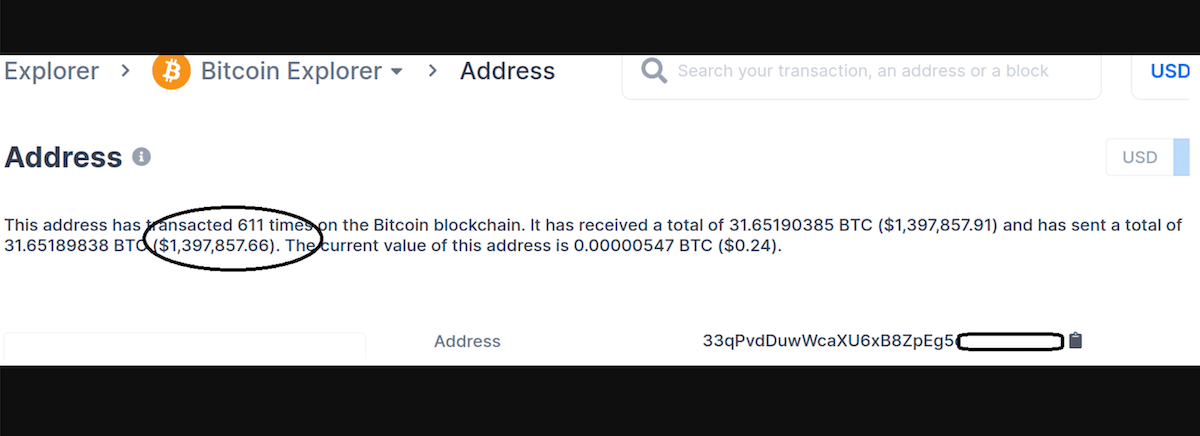
An account used by the scammer has over $1.3 million worth of Bitcoin stolen from unsuspecting victims.
One of the victims shared the bitcoin address to which they transferred their money, and when we checked at the time of writing it has been sent over $1.39 million dollars to date. This shows the scale of this scam and how much money fraudsters are making from vulnerable users. This is just one bitcoin address, the tip of the iceberg. There could be several, with millions being lost.
The researchers conclude that even with Fleeceware, App Store is a safe marketplace for iPhone users to download apps because scams like “CryptoRom bypasses all of the safety screening of the App Store and instead targets vulnerable iPhone victims directly” and demand that “Apple should warn users installing apps through ad hoc distribution or through enterprise provisioning systems that those applications have not been reviewed by Apple” to reduce the risk of these scams.
This is exactly what Apple has been warning regulators about who are demanding that the company should allow sideloading on iOS devices. Sideloading which will give unchecked apps access to iPhones will have devasting impact on users’ privacy and security.
Read More:
- Apple says Android devices have 15 to 47 times more malware infections than iPhone because of sideloading
- Apple Head of User Privacy explains the negative impact of ‘sideloading’ on iOS and iPadOS
- Apple restores ‘Report a Problem’ option App Store to flag scam apps and other issues
- Updated App Store guidelines make ‘account deletion within apps’ mandatory
- Apple dedicates ‘Developing for App Store’ section on website to developers



