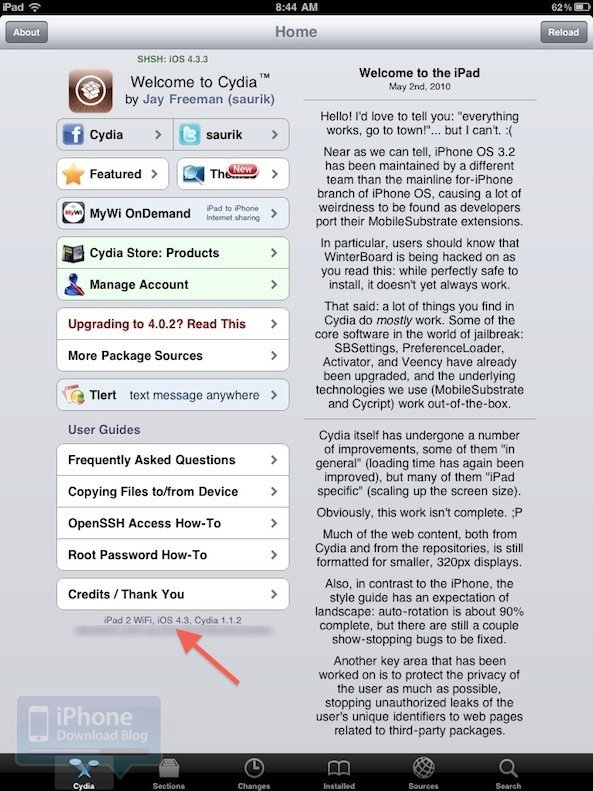
You all must know by now that a beta tester for JailbreakMe 3.0 leaked some iPad 2 jailbreak files from @Comex‘s upcoming not-so-secret project. The jailbreak files were available online for a brief period before they were taken down permanently. However, a hacker named Ryan Vanniekerk managed to grab those files during that short window and has now put up a complicated guide on how to use these leaked files to “set up your own web-based exploit” and jailbreak all current devices including the iPad 2 running iOS 4.3.3.
The hacker has published a detailed how-to on his personal blog:
After a bit of digging I happened across a relatively inconspicuous comment that lead me to believe that the “unable to download jailbreak files” was attempting to connect directly to Comex’s server (located at 157.22.252.87) in order to download the existing jailbreak files. However, the files attempting to be downloaded were the exact same files that had already been leaked earlier in the day, they simply existed in a separate location.
My first thought was to spoof a local webserver with the same IP that the jailbreak is connecting to in order to make it look for the files there instead. After a bit of tinkering around I finally managed to bypass the 403 error and successfully jailbreak my iPad 2!”
It is almost certain that JailbreakMe 3.0 would go online pretty soon (hopefully tonight) since you get a “we’ll be back soon!” sticky if you access the jailbreakme.com website right now, hinting at an imminent release. Therefore, it is not recommended at all to try out an unstable release of iPad 2 jailbreak when the real thing is just around the corner!
Subscribe to our RSS Feed and keep following us on Twitter, Facebook and YouTube for all the latest news, updates and more.
[via iPDb]



